Recent research by the cybersecurity company Resecurity has revealed that legacy Windows protocols remain a significant vector for credential theft within organizations. Despite advancements in digital security, many companies continue to use these outdated systems, making them easy targets for cyber attackers.
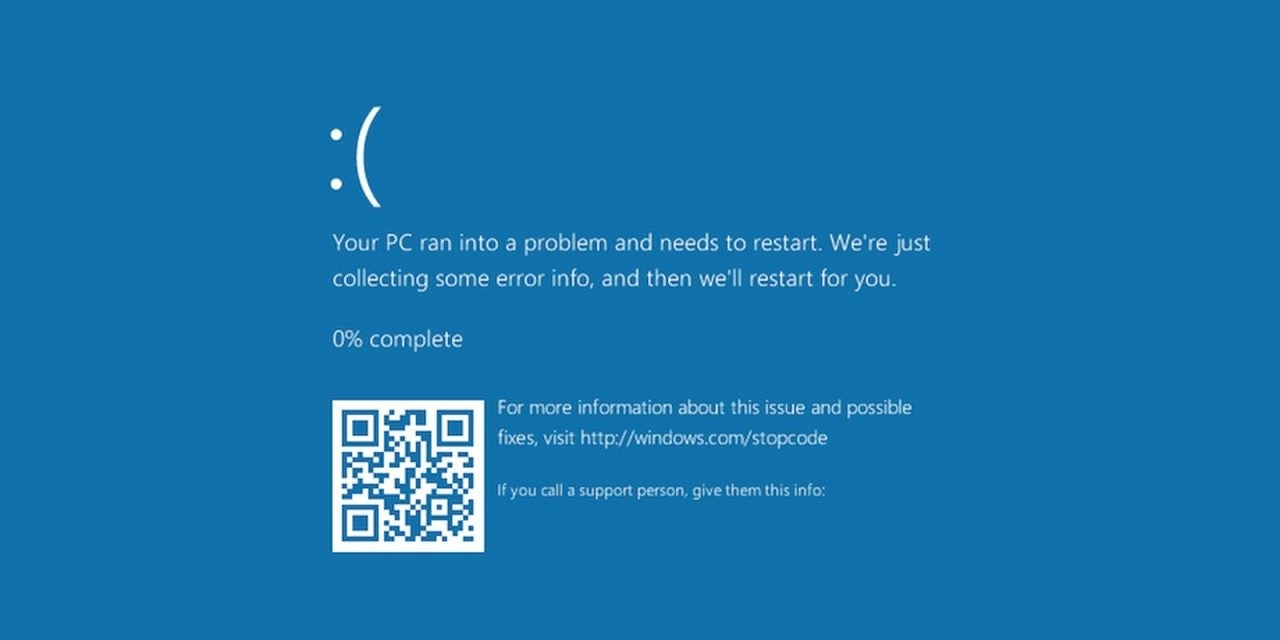
Your operating system is the weakest part of your organization
Systems that use these old protocols have vulnerabilities that can be exploited by cybercriminals to gain unauthorized access to corporate networks. Resecurity has highlighted that the attack methods are varied, including password manipulation and the exploitation of authentication flaws. This situation is exacerbated by the fact that many organizations are unaware of the risks associated with using these systems, which were designed in an era when cyber threats were much less sophisticated.
The research has highlighted the urgent need to modernize IT infrastructures. Recommendations include the implementation of more secure authentication systems and the use of current protocols that are more resistant to attacks. Resecurity has also emphasized the importance of ongoing education for employees in security matters, as the human factor remains one of the biggest vulnerabilities in cybersecurity.
Additionally, it has been mentioned that some organizations may be driven to adopt new technologies and security practices in response to this type of threat, which could lead to a significant change in the way companies manage their digital operations. However, the risk persists as long as legacy protocols remain, and experts warn that the protection of data and critical infrastructure depends on a prompt adaptation to best practices in cybersecurity.