With the traditional approach to security, tools focus on what’s going on within your network. NordStellar, however, takes a modern approach and understands that risks also come from outside your defined perimeter, where your EDRs and SIEMs have no reach. We’re talking about the spaces where hackers are trading your data, planning attacks, and scanning your online footprint.
The dark web, for instance, is a well-known source for such activities. Sites here sell stolen data, where items like stealer logs are being sold as a hot commodity—bundles of data taken from compromised devices by malware that steals login credentials or session cookies. In fact, something as simple as a cookie with a login status can sometimes be used to bypass passwords altogether and even Multi-Factor Authentication (MFA).

Another risk is what’s known as your external attack surface, and it consists of all the organization’s internet-facing assets. There’s also cybersquatting, where registered lookalike domains can trick users into clicking on fake links. So while you might have the best protection on your network, if you’re not looking outside, there are still very real and very significant risks to your business.
Common external threats include employee credentials ending up on forums, cookie sessions being sold, phishing scams using your brand, and forgotten subdomains compromised due to open ports.
These attacks can be every bit as devastating as internal attacks. A stolen account can lead to financial fraud. Data sold on the dark web leads to unauthorized access for network attacks and leaks. Lookalike domains hurt user trust. Finally, unpatched systems provide a pathway for ransomware. These all may result in regulatory exposure and expense.
How NordStellar Protects Outside Your Perimeter
NordStellar is a threat exposure management platform, which means it looks for danger in places you do not control. It continuously scans external sources such as criminal forums on the dark web, ransomware blogs, Telegram channels, and other sources for signs that your company, people, or assets are being targeted.
You define the scope. Add your domains, brand names, executive names, project code names, partner identifiers, and IP addresses. NordStellar then correlates what it finds with your scope, adds context, and ranks issues by risk so the most urgent items rise to the top. This is the same risk-first behavior reviewers describe when they note alerts are sorted by severity and the platform covers attack surface management.

When something relevant appears, you receive an alert with the source link, the timestamp, and who or what is at risk. You can deliver these alerts to email, Slack, Microsoft Teams, and other applications via custom webhooks or route them to your SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) through the API.
The practical outcome is faster decisions and fewer surprises. Teams spot leaked credentials before they are abused, catch lookalike domains before a phishing run, and uncover exposed assets on the public internet that internal scanners have not flagged yet. Third-party summaries in 2025 highlight this outside-in visibility as a core strength of the platform.
How to Set It Up
- Add what to watch. Enter monitored domains, brand names, VIP identities, partner names or domains, and IP addresses. Automated asset discovery and mapping is available to speed this step.
- Connect where alerts should go. As mentioned, you can link email, Slack, Teams, and your security stack. If your team works from a SIEM or SOAR, enable the API integration so alerts and context flow into the tools you already use.
- Let the system run and triage. NordStellar continuously collects signals and assigns a risk level to each finding. Findings can be reviewed, assigned, and tracked to resolution using your existing SIEM or other workflow management tools.
NordStellar’s Key Capabilities
NordStellar provides real-time protection that detects, monitors, and helps you respond to external threats before they escalate. Here are just a few of the many ways that this comprehensive solution will keep your company safe.
Data Breach Monitoring
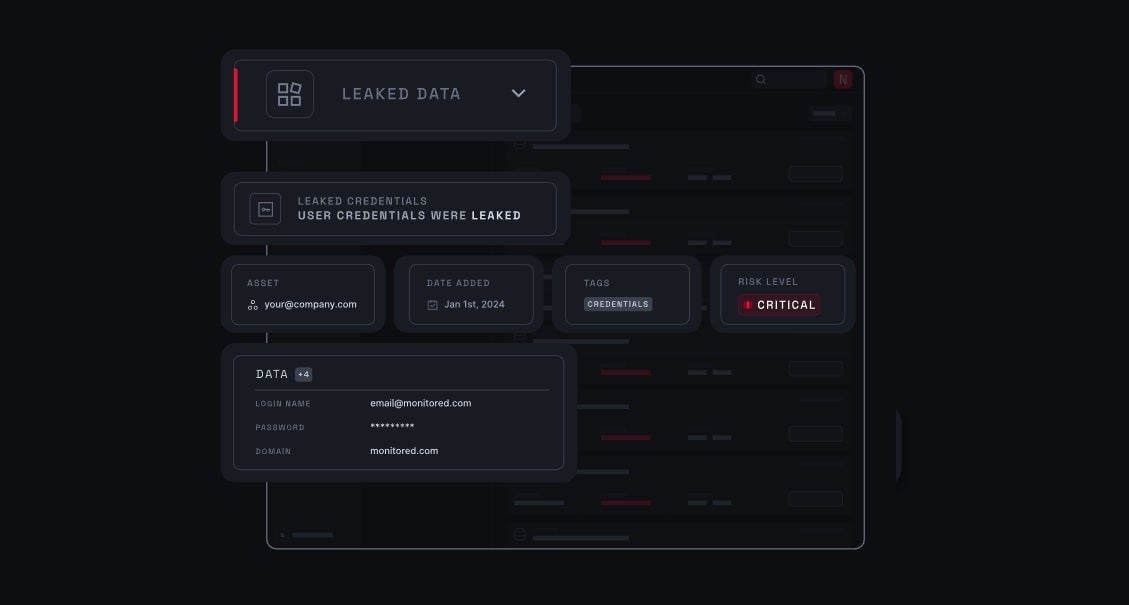
NordStellar’s approach to data breach monitoring focuses on detecting data breach dumps, combo lists, and infostealer logs such as those that include active session cookies, as well as stolen credentials and Personally Identifiable Information (PII).
As mentioned, because session cookies alone can let an attacker skip passwords and MFA entirely, it’s vital to catch these. With a valid cookie, an attacker can behave like a user in your organization until their access is revoked. That means a basic infection on any home device can become a huge business risk.
Alerts from the data breach monitoring feature log where data was found, when, and the domains and services involved.
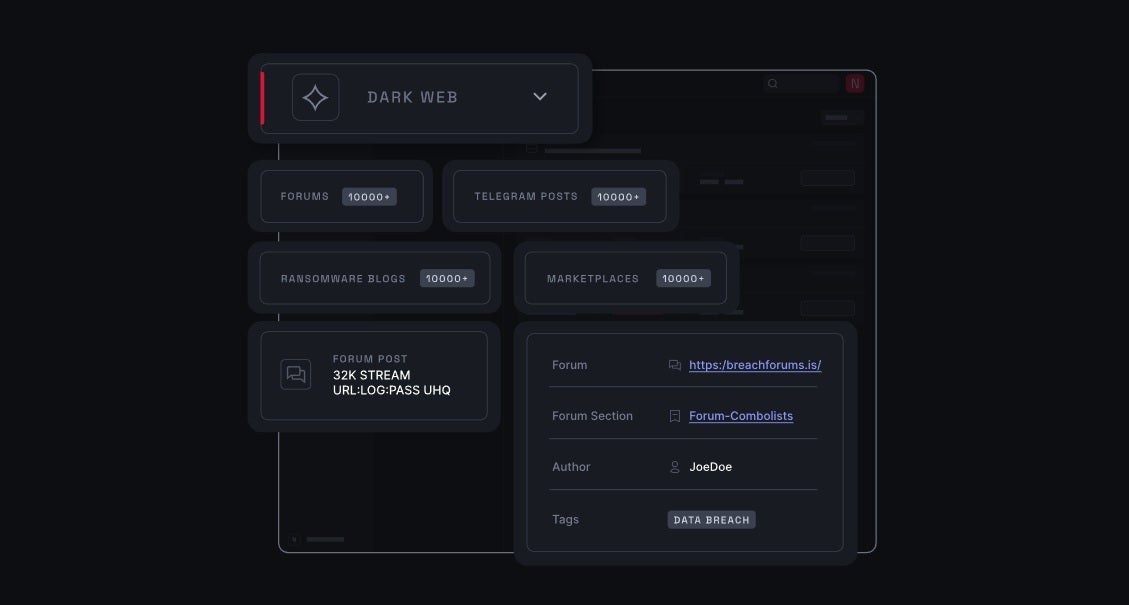
Dark Web Monitoring
This feature tracks forums and listings online that include targeting or data leaks. NordStellar’s coverage extensively includes marketplaces, ransomware blogs, forums, and Telegram channels. If something is spotted, you’re alerted in real time from a predefined keyword list that you manage.
This keyword list includes things like your brand, product names, executives, partners, and internal project codenames. Any asset that you want to protect. This coverage extends to over 40,000 sources, and results include source and context, which you or your analysts can verify.
This will give you the opportunity to learn about breaches and leaks of stolen credentials early, and you may even catch planned phishing and lookalike domains before they affect users
Alerts are handy because they include the post’s content, author, and exposure time.
Attack Surface Management
Attack Surface Management identifies and evaluates internet-facing assets. NordStellar inventories your organization’s domains, subdomains, and IP addresses, fingerprinting technologies and finding weaknesses.
Common issues detected include open ports, software versions with known vulnerabilities, forgotten sites, and misconfigurations. Information about vulnerabilities includes detected CVEs, CVSS scores, and affected ports and services.
Because NordStellar uses passive techniques, it complements internal vulnerability scanners and agent-based tools. It shows what attackers can see.
NordStellar uses automated discovery, DNS enumeration, passive scanning, and crawling to keep inventories up to date. Alerts are sent instantly as vulnerabilities or new open ports are detected. The current scope does not include deep cloud environment scanning, so it should be paired with cloud-native tools as well. Depending on your structure, it’s worth reviewing asset findings weekly with app teams and integrating results in CMDB.
Cybersquatting Detection
Cybersquatting Detection finds spoofed domains that mimic your brand. NordStellar uses content and visual similarity models, as well as hosting, DNS, and IP indicators, to assess risk.
Detections cover misspellings, homoglyphs, and added words. It also renders sites to detect mimicked login pages and phishing. You get clean alerts that include registrars, hosting, and screen captures for fast review.
A suggested action plan helps you respond. Validate intent, notify registrars, and request takedown in cases of clear abuse.

Brand Protection Add-on
Brand Protection is an optional add-on that widens monitoring to the open web, social networks, and mobile app stores. It looks for abuse of your brand, such as lookalike domains, fake pages and profiles, and cloned or malicious apps that try to pass as yours.
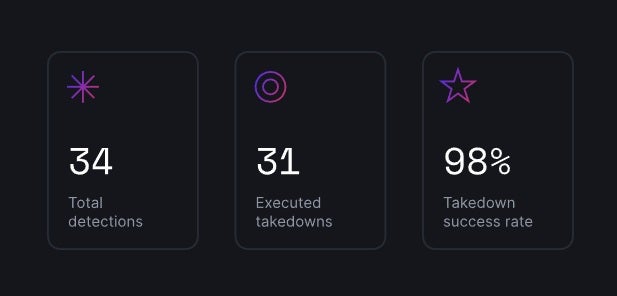
The service includes a managed response. When NordStellar confirms an incident, it initiates takedowns, which means filing formal removal requests with the domain registrar, hosting provider, social platform, or app store to pull down the offending content. You receive periodic reports that list each case, what was removed, and the current status.
This add-on was introduced in October 2025 and is now part of NordStellar’s portfolio.
Results You Can Measure in 90 days
NordStellar can make a measurable difference to your security in a very short space of time.
Proactive protection enables you to detect risks faster. Stolen credentials, session cookies, phishing domains, and exposed systems don’t go unnoticed, so incidents are mitigated faster. Comprehensive visibility reduces risks by leveraging one of the broadest external data pools, with 40,000-plus sources, 90 billion-plus leaked credentials, and 50 million-plus stealer logs analyzed.
Incident context is provided in alerts, so you know exactly where it was observed and its potential impact. Faster detection and means of validation result in a reduction in time to respond.
Start Now and Get the Black Friday Offer
Get started with NordStellar by taking advantage of its Black Friday offer while it lasts. Sign up, configure your top domains, brands, VIPs, and assets, and set delivery to inbox, Slack, and SIEM. Set up your 1st proof-of-value test and see risk cases within days.
Don’t wait for your data to show up on a forum. Start monitoring now to avoid threats from outside your perimeter.
