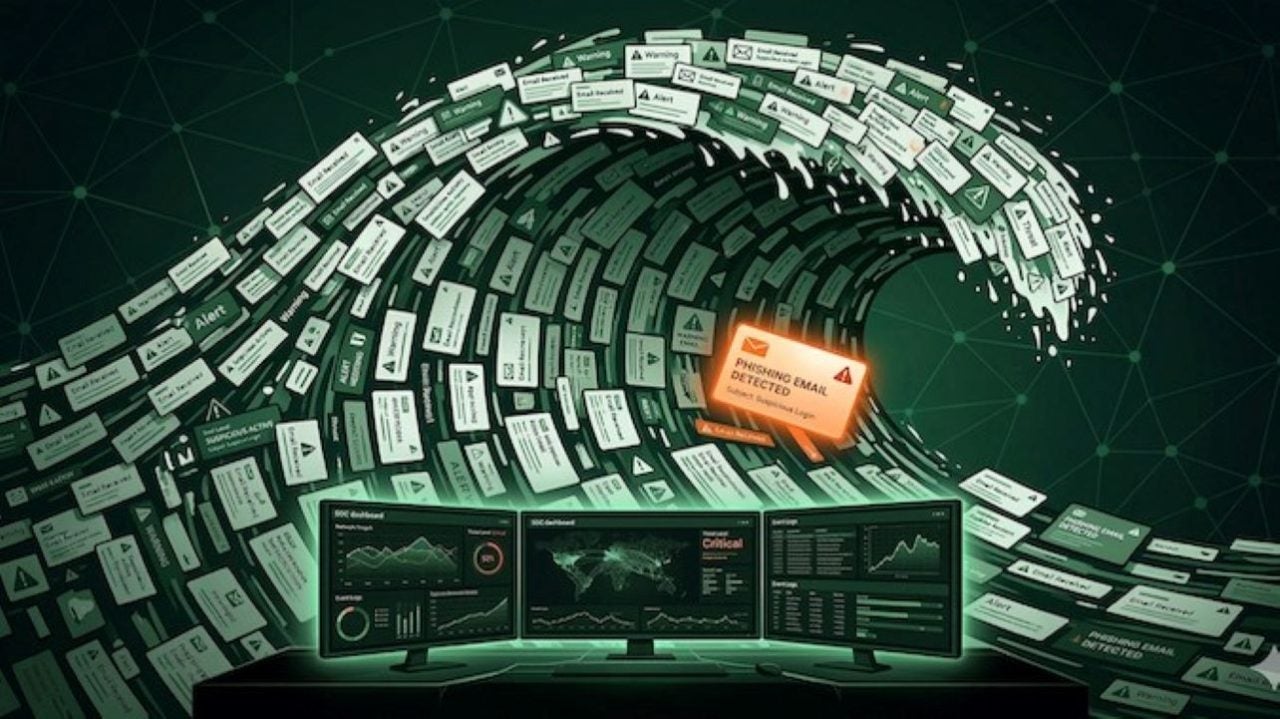
Phishing campaigns have become more sophisticated, not only seeking to deceive employees but also exhausting the resources of security operations analysts (SOC). Organizations are facing an increase in phishing reports that congest investigation queues, which decreases the quality of analysis and increases the risk of security breaches.
Fishing in the Sea of Crime
According to recent reports, some attackers have designed their campaigns to maximize the effort required for investigation, causing incidents that should be resolved in minutes to take hours, significantly widening the window of opportunity for an attack. This tactic has led SOC teams to a state of alert fatigue, where response times are reduced and decisions are made with less rigor.
Organizations, therefore, must reevaluate their approaches to defending against phishing. It is not only about training employees to identify suspicious emails, but also about optimizing post-report investigation processes. Implementing systems that provide synthesized analysis can enable analysts to make faster and more effective decisions, reducing investigation time from hours to minutes.
Despite current efforts to automate threat detection, many tools do not address the fundamental problem of workload in SOCs. An emerging approach is focused on decision-ready investigation, where the system provides a clear assessment, allowing analysts to review investigations instead of conducting them from scratch. This could radically change the dynamics of investigations against phishing campaigns, contributing to a faster and more robust response to attacks.
Platforms like Conifers.ai are developing solutions to provide these phishing investigations in minutes, instead of hours, effectively combating the attackers’ exhaustion strategies.