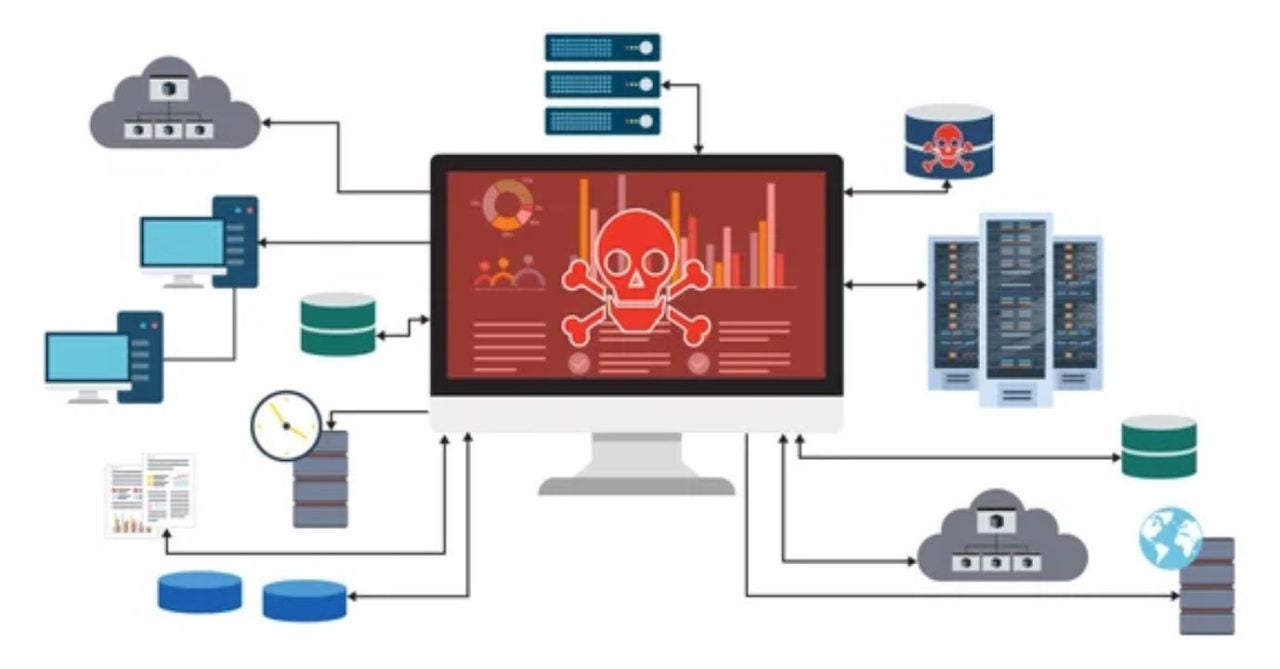
Recently, there has been an increase in the activities of groups of individuals using malicious strategies to compromise the security of users’ computer systems. These threat actors employ various tactics to deceive people, which has led to a significant increase in the installation of unauthorized remote access tools. These tools, although designed to facilitate the control and management of systems remotely, can be maliciously used by attackers to access sensitive information or take control of devices.
The danger of working from home
The most common methods to attract users to install RMM software include phishing and the appearance of misleading offers. Some cybercriminals use emails that appear to be official communications from recognized companies, while others may create ads that promise free solutions or significant discounts on technology products. These tactics aim to exploit the user’s curiosity or need, leading them to execute programs that compromise their security.
Additionally, it is important to highlight that the proliferation of these methods has also been encouraged by the growing dependence of users on digital technologies during the pandemic. With more people working from home, many are unaware of the dangers associated with software that allows remote access. The unintentional installation of these tools can lead to serious intrusions, compromising both personal data and corporate information.

Cybersecurity experts warn that it is always advisable to verify the authenticity of any software you wish to install and to be wary of offers that seem too good to be true. Prevention becomes the first line of defense against these emerging threats that, unfortunately, continue to rise.