When LastPass disclosed a security breach in August 2022, it sounded harmless enough at first. The attacker managed to obtain proprietary information and source code, but no customer data.
When the same threat actor used the obtained data to attack the company again, things still did not look too bad. The attack on storage volumes within the company’s cloud-based storage service gave the attacker access to user information, but not the password vaults of customers. At least, that is what LastPass concluded after its initial investigation.
Today, LastPass confirmed that the second hack was more serious than initially thought. A security notice on the company’s official blog confirms that the attacker obtained customer information and password vault data.
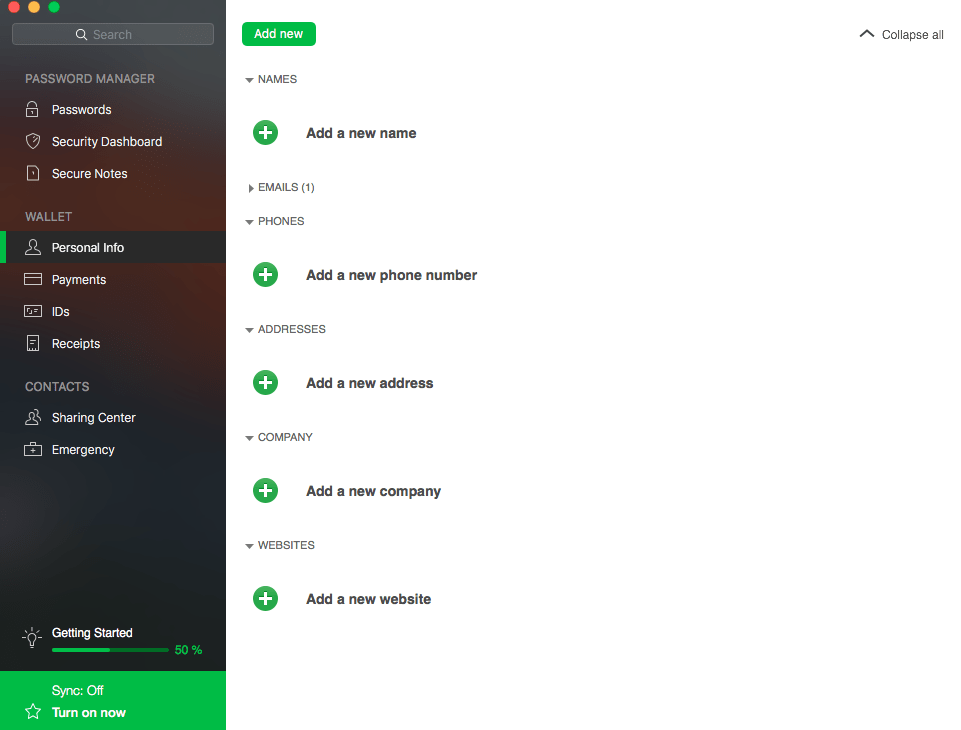
The following user data was copied by the attacker:
- Company and end-user names.
- Billing addresses.
- Email addresses.
- Telephone numbers.
- IP addresses.
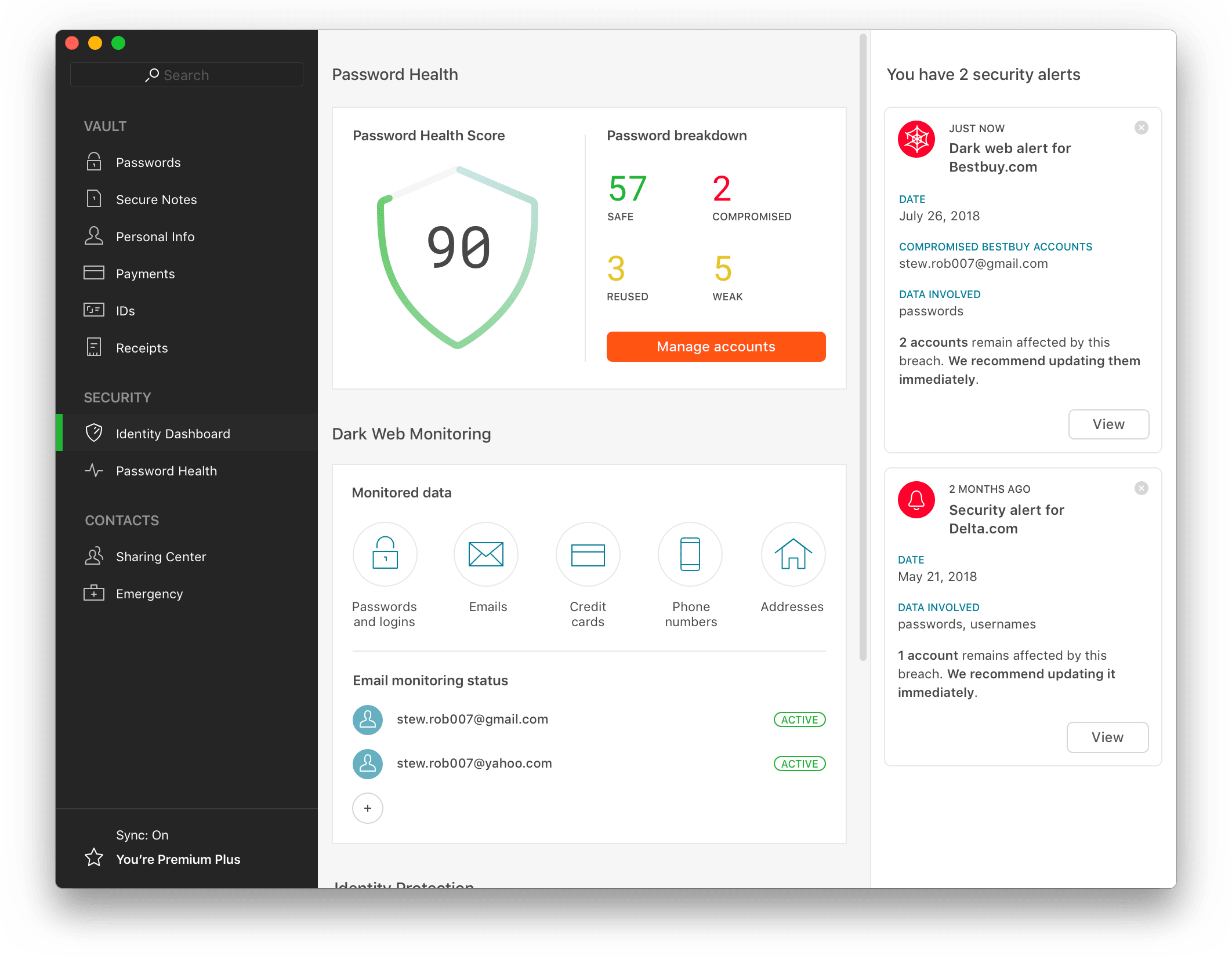
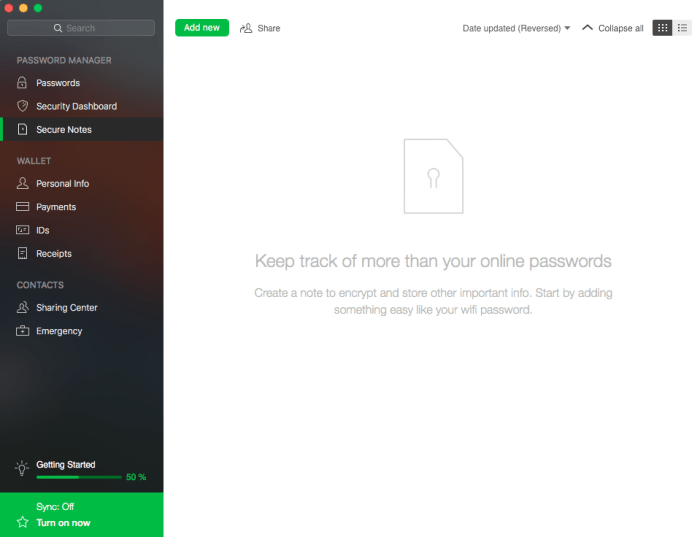
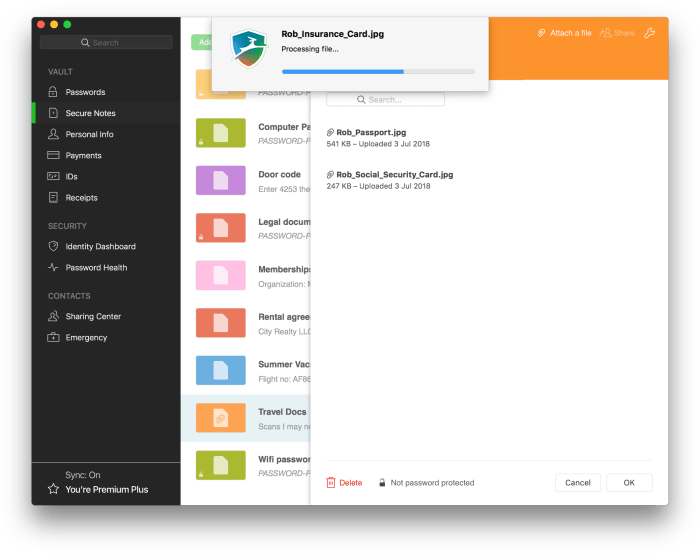
Next to that, the attacker managed to obtain a copy of a “backup of customer vault data from the encrypted storage container”. The information includes unencrypted data, such as website addresses, but also “fully encrypted sensitive fields”. These fields include website usernames and passwords, secure notes, and form-fill data.
LastPass found no evidence that unencrypted credit card data was accessed by the attacker. The company does not store “complete credit card numbers” according to the announcement.
The master password, which unlocks all customer data, is known only to the customer. LastPass does not store it and sensitive vault data is encrypted with 256-bit AES encryption.
Worst Case Scenario
This is the worst case scenario for LastPass customers. The plain text data includes means of communication, and the vault data all stored passwords and sensitive information.
The threat actor may attempt to brute force vault data, which would unlock usernames and passwords for all stored services. Successful attacks may also reveal information stored in secure notes. This may lead to compromised user accounts on the Web or company intranets.
Brute forcing attacks of this scale require vast resources, especially if carried out on such a large number of protected vaults. The attack was sophisticated, and it is not out of the question that the attacker has the required resources to run brute force attacks on the encrypted data obtained during the attack.
A strong master password may prevent successful brute force attacks. LastPass recommends master passwords with at least 12 mixed characters, but customers are free to select theirs during setup.
Next to brute force attacks, customers may also be attacked using phishing or social engineering attacks. The attacker may use these attacks to obtain the master password. Attacks may happen via email, telephone, chat messages, or even letters.
The attacker may impersonate LastPass in these attacks to get users to click on links or part with information directly.
What LastPass customers need to do right now
LastPass customers should assume that their information and vault data has been compromised. The following steps are recommended to secure the data:
- Change the LastPass master password. Make it unique and strong, e.g., with 16 or more random characters that include upper-case and lower-case letters, numbers and special characters.
- Change the number of password iterations from the default 100100 to 310000 or even more.
- Go through each saved login and change all passwords. Make each password strong and unique as well.
- Monitor emails, phone calls, chat messages and other forms of communication, and avoid clicking on links.
The process may take a while, especially if dozens or even hundreds of logins are stored in the LastPass vault.
Customers may also consider switching services. Password manager alternatives such as the open source Bitwarden service have not suffered data breaches up to this point. It is still necessary to change passwords.
Tip: check out our top 25 alternatives to LastPass.
Regardless of that, some information is in the attacker’s hands and there is nothing that customers may do about it.





 The software will walk you through the creation of an account and a strong master password.
The software will walk you through the creation of an account and a strong master password.